> The Curator's Exit
> CHALLENGE DESCRIPTION
We've received a communication from Interpol, containing a PDF. We are unsure of the contents, but believe it contains information on one of the thieves from the Louvre Heist. Your job is to find out as much as you can about this individual and send the information back to the authorities.
What is the thief's name?
FLAG FORMAT: CIT{First_Last}
[Attached Asset: VF0000000011-Enc.pdf]
> METHODOLOGY
1. Brute-Forcing the Encrypted PDF
The provided PDF dossier was encrypted. To access the contents, I first extracted the PDF hash and then ran it through hashcat using the rockyou.txt wordlist.
(venv) ⌘Ser!s ~/Downloads/ctf % hashcat -m 10700 -a 0 pdf_hash.txt /Users/seris/Downloads/ctf/rockyou.txt hashcat (v7.1.2) starting$pdf$56256*-411647db8ab1c98eba67d6d5048e52d292c148*8db75818…8b8c034b:cherell Session…: hashcat Status…: Cracked Hash.Mode…: 10700 (PDF 1.7 Level 8 (Acrobat 10 - 11)) Time.Started…: Sat Apr 18 19:16:36 2026 (5 mins, 54 secs) Speed.#02…: 532 H/s (26.63ms) @ Accel:21 Loops:1 Thr:224 Vec:1 Recovered…: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
The hashcat run successfully cracked the password: cherell.
2. Document Analysis & Username Extraction Unlocking the PDF revealed a “Subject Dossier” from the Cultural Property Risk Cell. Scanning the document, I identified the suspect’s primary alias.
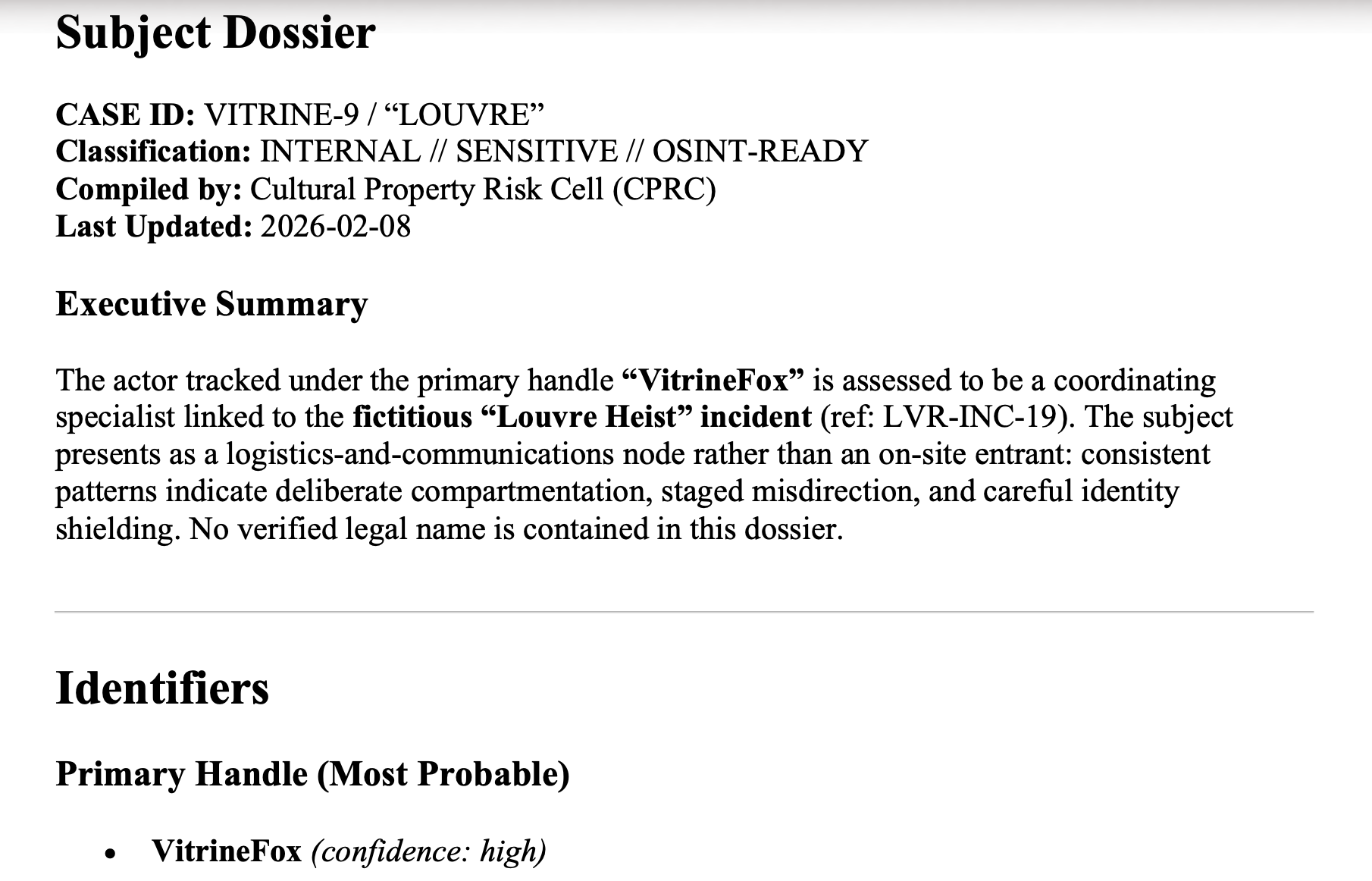
The most probable handle was listed as VitrineFox.
3. Username Enumeration (WhatsMyName)
With a solid handle, I moved to username enumeration. While sherlock via CLI is an option, I used the web-based tool WhatsMyNameApp for faster visual parsing. Searching for vitrinefox returned multiple active profiles across the web.
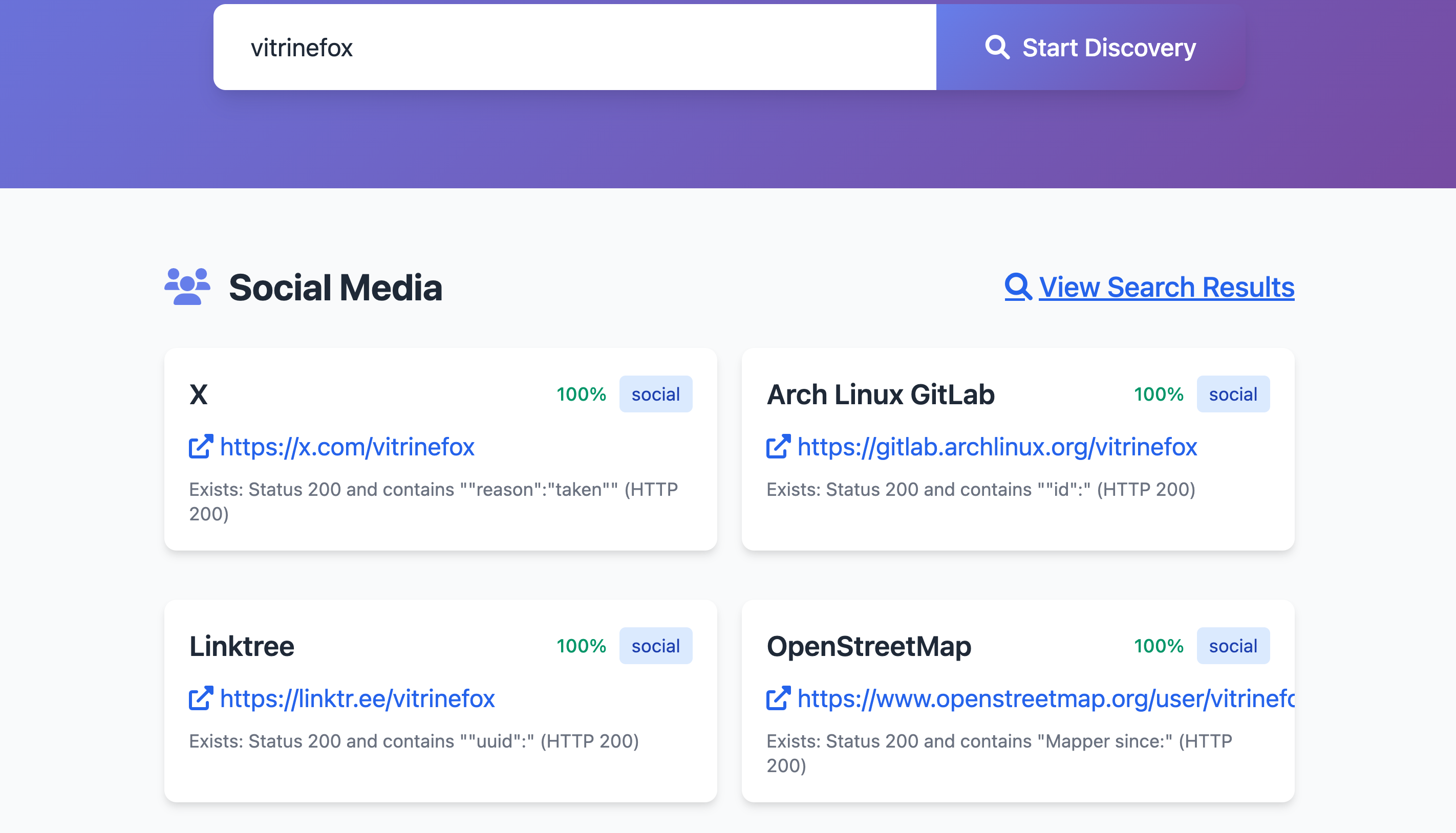
The results provided a crucial pivot point: a Linktree profile (linktr.ee/vitrinefox).
4. The Rabbit Hole & Social Media Pivoting The Linktree consolidated the target’s digital footprint, linking to their X (Twitter) account, a PCPartPicker profile, and a LinkedIn page.
I initially investigated the X account and found a post featuring an image of the birthplace of Leonardo da Vinci. I went down a rabbit hole trying to trace the origin of that image, discovering it was originally published by an author named “Sara Turini - Discover Tuscany Team”. I suspected she might be our culprit, but after digging further, I realized this was a complete dead end.
Recalibrating and remembering the other accounts listed on the Linktree, I pivoted to their LinkedIn profile (linkedin.com/in/vitrine-fox-424b153b3). Opening the “Contact info” modal revealed an exposed ProtonMail address.

The email address remy.beauvillier@proton.me clearly exposes the thief’s real first and last name.
> THE FLAG
Extracting the names from the email address and formatting them as requested:
CIT{Remy_Beauvillier}